WS2022
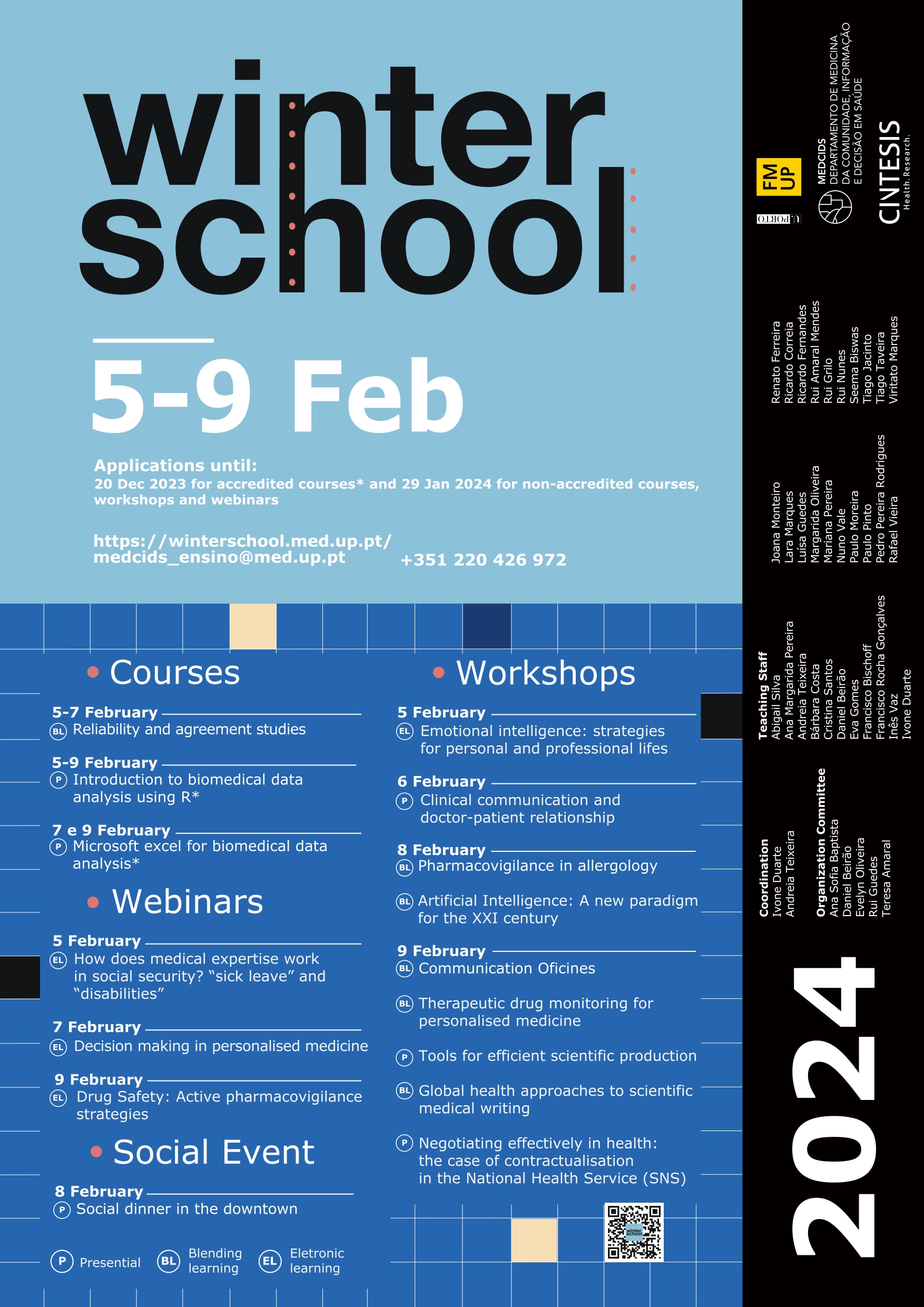
As candidaturas para a Winter School já estão abertas, com cursos, workshops e webinars, vem conhecer melhor a Winter School deste ano.
Licenciatura SDIB
Social Media
2 months ago
A Clínica FMUP abre portas pela primeira vez. 🩺![]()
![]() "Somos uma clínica orientada para a prestação dos cuidados de saúde que cada um necessita, com foco especial na prevenção das doenças, na inovação e no respeito pelas expectativas individuais, e para a obtenção de resultados em saúde na comunidade."
"Somos uma clínica orientada para a prestação dos cuidados de saúde que cada um necessita, com foco especial na prevenção das doenças, na inovação e no respeito pelas expectativas individuais, e para a obtenção de resultados em saúde na comunidade."![]()
![]() Pode saber mais no link da Bio ou contactar-nos pelos meios disponíveis. 📱
Pode saber mais no link da Bio ou contactar-nos pelos meios disponíveis. 📱![]()
![]() #clinicafmup #saude #prevenção #medicina
... See MoreSee Less
#clinicafmup #saude #prevenção #medicina
... See MoreSee Less
3 months ago
Último dia para se inscrever na Winter School 2024!![]()
![]() Pode inscrever-se em cursos, workshops e webinars gratuitos em s.up.pt/fvcy
Pode inscrever-se em cursos, workshops e webinars gratuitos em s.up.pt/fvcy![]()
![]() As formações serão dadas em Português.
... See MoreSee Less
As formações serão dadas em Português.
... See MoreSee Less
3 months ago
Vaga para novo colaborador![]()
![]() No âmbito da Cátedra Convidada de Inovação em Oncologia da Faculdade de Medicina da Universidade do Porto, encontra-se aberto a contratação de um colaborador que tenha experiência em pelo menos uma das seguintes áreas:
No âmbito da Cátedra Convidada de Inovação em Oncologia da Faculdade de Medicina da Universidade do Porto, encontra-se aberto a contratação de um colaborador que tenha experiência em pelo menos uma das seguintes áreas:![]()
![]() - Marketing digital
- Marketing digital![]() - Gestão de projetos
- Gestão de projetos![]() - Tecnologias digitais
- Tecnologias digitais![]() - Inovação em saúde
- Inovação em saúde![]() - Atividades de secretariado
- Atividades de secretariado ![]()
![]() A manifestação de interesse deve ser através do envio de um e-mail para:
A manifestação de interesse deve ser através do envio de um e-mail para:![]() nunovale@med.up.pt e catedraoncologia@med.up.pt
nunovale@med.up.pt e catedraoncologia@med.up.pt ![]()
![]() Com anexo do CV e certificado de habilitações. O prazo para a receção de manifestações de interesses termina às 23h59 do dia 25 de janeiro de 2024. Os candidatos selecionados serão convidados para a realização de uma entrevista antes da seriação final. A contratação será em regime de prestação de serviços com base nas habilitações do candidato. O início de atividade será em fevereiro de 2024.
... See MoreSee Less
Com anexo do CV e certificado de habilitações. O prazo para a receção de manifestações de interesses termina às 23h59 do dia 25 de janeiro de 2024. Os candidatos selecionados serão convidados para a realização de uma entrevista antes da seriação final. A contratação será em regime de prestação de serviços com base nas habilitações do candidato. O início de atividade será em fevereiro de 2024.
... See MoreSee Less
3 months ago
Últimos dias das candidaturas ao BLICS.![]() Para mais informações:
... See MoreSee Less
Para mais informações:
... See MoreSee Less
BLICS – Blended Learning Intoduction to Clinical Studies
blics.med.up.pt
Bem Vindo ao BLICS O BLICS é um curso b-learning de investigação clínica do Departamento de Medicina da Comunidade, Informação e Decisão em Saúde (MEDCIDS) da Faculdade de Medicina da Universi...4 months ago
Nova edição do curso «Telemedicina e e-saúde» ![]()
![]() Candidaturas abertas de 2 a 17 de janeiro de 2024
Candidaturas abertas de 2 a 17 de janeiro de 2024![]()
![]() Para mais informações: sigarra.up.pt/fmup/pt/noticias_geral.ver_noticia?p_nr=92139
... See MoreSee Less
Para mais informações: sigarra.up.pt/fmup/pt/noticias_geral.ver_noticia?p_nr=92139
... See MoreSee Less
4 months ago
FMUP organiza seminários sobre os cuidados de saúde primários![]()
![]() A Faculdade de Medicina da Universidade do Porto (FMUP) irá promover um ciclo de seminários abertos sobre o tema dos cuidados de saúde primários (CSP).
A Faculdade de Medicina da Universidade do Porto (FMUP) irá promover um ciclo de seminários abertos sobre o tema dos cuidados de saúde primários (CSP).![]()
![]() Organizada no âmbito do Mestrado em Cuidados de Saúdes Primários, a iniciativa arranca já no dia 4 de janeiro (quinta-feira), às 17 horas, com uma palestra sobre a multimorbilidade nesta área, com a participação de Bruno Heleno.
Organizada no âmbito do Mestrado em Cuidados de Saúdes Primários, a iniciativa arranca já no dia 4 de janeiro (quinta-feira), às 17 horas, com uma palestra sobre a multimorbilidade nesta área, com a participação de Bruno Heleno.![]()
![]() No dia seguinte, 5 de janeiro, o programa inicia às 14 horas, com a participação de Deoclécio Avigo, numa sessão intitulada “Atenção Primária no Brasil”. Às 15h30, será a vez de Sofia Baptista falar sobre “A arte no Ensino Médico” e mais tarde, às 17 horas, Daniel Dias irá abordar o “Mapeamento de evidência em cuidados de saúde primários”.
No dia seguinte, 5 de janeiro, o programa inicia às 14 horas, com a participação de Deoclécio Avigo, numa sessão intitulada “Atenção Primária no Brasil”. Às 15h30, será a vez de Sofia Baptista falar sobre “A arte no Ensino Médico” e mais tarde, às 17 horas, Daniel Dias irá abordar o “Mapeamento de evidência em cuidados de saúde primários”.![]()
![]() O ciclo de seminários abertos retoma no dia 11 de janeiro com uma nova sessão tripla de palestras. Inicia-se às 14 horas com a “Literacia em Saúde” (Paulo Santos), depois às 15h30 com a “História da Assistência Médica no Porto” (Joel Cleto) e às 17h com a “Evolução histórica dos cuidados de saúde primários em Portugal” (Jaime Correia de Sousa).
O ciclo de seminários abertos retoma no dia 11 de janeiro com uma nova sessão tripla de palestras. Inicia-se às 14 horas com a “Literacia em Saúde” (Paulo Santos), depois às 15h30 com a “História da Assistência Médica no Porto” (Joel Cleto) e às 17h com a “Evolução histórica dos cuidados de saúde primários em Portugal” (Jaime Correia de Sousa).![]()
![]() Os seminários terminam no dia 12 de janeiro com uma sessão dupla, às 16 horas com a participação de Catarina Oliveira sobre a “Investigação clínica em CSP” e às 18 horas com Válter Fonseca sobre o “Desenvolvimento de orientações clínicas”.
Os seminários terminam no dia 12 de janeiro com uma sessão dupla, às 16 horas com a participação de Catarina Oliveira sobre a “Investigação clínica em CSP” e às 18 horas com Válter Fonseca sobre o “Desenvolvimento de orientações clínicas”.![]()
![]() Todos os seminários têm transmissão em direto aqui:
... See MoreSee Less
Todos os seminários têm transmissão em direto aqui:
... See MoreSee Less
Faculdade de Medicina Universidade do Porto - YouTube
www.youtube.com
198 anos de dedicação ao Ensino e InvestigaçãoA Medicina começa aqui! 🎓